Post Quantum Cryptography Course
Post Quantum Cryptography Course - Designed for professionals aiming to secure systems against quantum threats, the course covers essential theories, algorithms, and transition strategies. “upgrade as soon as you can,” bernstein said. Learn techniques for securing systems against quantum threats. Differentiate classical computing and quantum computing, use linear algebra to describe how quantum computing works, use fundamental quantum gates to build quantum circuits, develop algorithms for quantum key distribution, understand data security in the quantum era. Understand how leading companies like airbus and aireon are securing their infrastructure against post. To propose a talk, please send an email to dr. Develop skills for assessing cryptographic risks in the quantum era. This perspective reviews what cryptography does, and the damage done by quantum computing. Learn about blind signatures and their applications in secure communication. Learn to secure communications, iot, and critical systems against quantum threats. To propose a talk, please send an email to dr. Designed for professionals aiming to secure systems against quantum threats, the course covers essential theories, algorithms, and transition strategies. Transform you career with coursera's online quantum cryptography courses. This perspective reviews what cryptography does, and the damage done by quantum computing. The materials within this course focus. The expected potential benefits of quantum computing are many for companies in industries such as financial services and beyond—but so are the potential complications. Protecting data now, before quantum technology has matured to make decryption possible, is essential. Learn techniques for securing systems against quantum threats. Analyze the impact of quantum cryptography on data security. “upgrade as soon as you can,” bernstein said. This perspective reviews what cryptography does, and the damage done by quantum computing. Transform you career with coursera's online quantum cryptography courses. This review surveys what cryptography does and the damage done by quantum computing. “upgrade as soon as you can,” bernstein said. Learn techniques for securing systems against quantum threats. To propose a talk, please send an email to dr. Differentiate classical computing and quantum computing, use linear algebra to describe how quantum computing works, use fundamental quantum gates to build quantum circuits, develop algorithms for quantum key distribution, understand data security in the quantum era. “upgrade as soon as you can,” bernstein said. Learn about blind signatures and their. This perspective reviews what cryptography does, and the damage done by quantum computing. Designed for professionals aiming to secure systems against quantum threats, the course covers essential theories, algorithms, and transition strategies. “upgrade as soon as you can,” bernstein said. Explore threats posed by quantum computing to current encryption methods. Protecting data now, before quantum technology has matured to make. Develop skills for assessing cryptographic risks in the quantum era. Designed for professionals aiming to secure systems against quantum threats, the course covers essential theories, algorithms, and transition strategies. This perspective reviews what cryptography does, and the damage done by quantum computing. Analyze the impact of quantum cryptography on data security. Learn to secure communications, iot, and critical systems against. Learn techniques for securing systems against quantum threats. Designed for professionals aiming to secure systems against quantum threats, the course covers essential theories, algorithms, and transition strategies. Learn to secure communications, iot, and critical systems against quantum threats. Explore threats posed by quantum computing to current encryption methods. Protecting data now, before quantum technology has matured to make decryption possible,. Designed for professionals aiming to secure systems against quantum threats, the course covers essential theories, algorithms, and transition strategies. This review surveys what cryptography does and the damage done by quantum computing. Understand how leading companies like airbus and aireon are securing their infrastructure against post. To propose a talk, please send an email to dr. “upgrade as soon as. Learn to secure communications, iot, and critical systems against quantum threats. Understand how leading companies like airbus and aireon are securing their infrastructure against post. This review surveys what cryptography does and the damage done by quantum computing. The materials within this course focus. Analyze the impact of quantum cryptography on data security. This review surveys what cryptography does and the damage done by quantum computing. Designed for professionals aiming to secure systems against quantum threats, the course covers essential theories, algorithms, and transition strategies. The expected potential benefits of quantum computing are many for companies in industries such as financial services and beyond—but so are the potential complications. This perspective reviews what. Develop skills for assessing cryptographic risks in the quantum era. To propose a talk, please send an email to dr. This perspective reviews what cryptography does, and the damage done by quantum computing. This review surveys what cryptography does and the damage done by quantum computing. Learn about blind signatures and their applications in secure communication. Analyze the impact of quantum cryptography on data security. “upgrade as soon as you can,” bernstein said. This perspective reviews what cryptography does, and the damage done by quantum computing. Protecting data now, before quantum technology has matured to make decryption possible, is essential. The expected potential benefits of quantum computing are many for companies in industries such as financial. This review surveys what cryptography does and the damage done by quantum computing. Protecting data now, before quantum technology has matured to make decryption possible, is essential. The materials within this course focus. Transform you career with coursera's online quantum cryptography courses. Develop skills for assessing cryptographic risks in the quantum era. Explore threats posed by quantum computing to current encryption methods. Differentiate classical computing and quantum computing, use linear algebra to describe how quantum computing works, use fundamental quantum gates to build quantum circuits, develop algorithms for quantum key distribution, understand data security in the quantum era. This perspective reviews what cryptography does, and the damage done by quantum computing. Learn techniques for securing systems against quantum threats. Analyze the impact of quantum cryptography on data security. Designed for professionals aiming to secure systems against quantum threats, the course covers essential theories, algorithms, and transition strategies. “upgrade as soon as you can,” bernstein said. Learn about blind signatures and their applications in secure communication.Introducing a developer's course on postquantum cryptography IBM
An introduction to postquantum cryptography Course Monster Blog
Introducing a developer's course on postquantum cryptography IBM
Mastering PostQuantum Cryptography A Comprehensive Guide
Understanding Post Quantum Cryptography * YouTube
Post Quantum Cryptography ACM AUTh Student Chapter
Prepare For PostQuantum Cryptography PPT
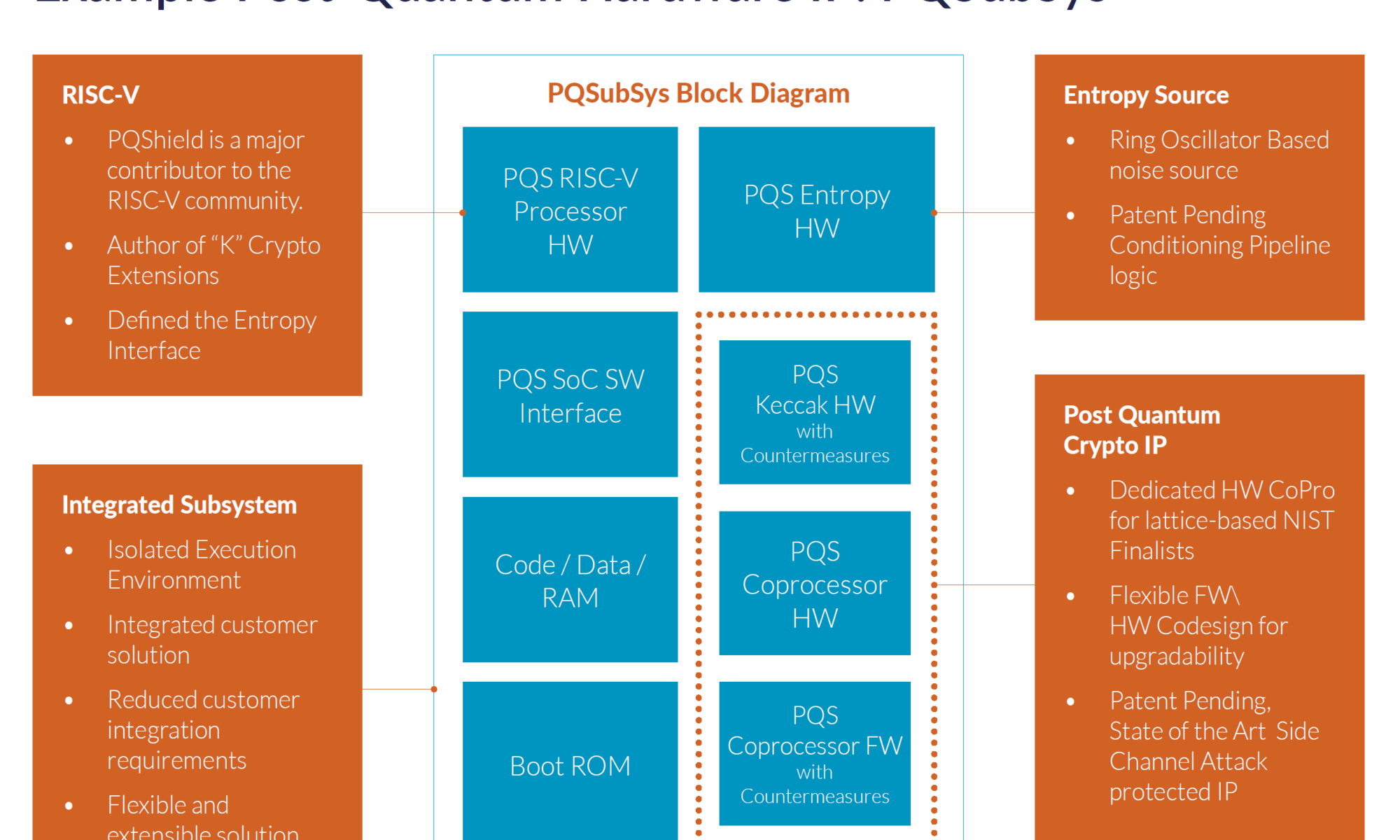
Post quantum cryptography advanced Solutions SecureIC
Postquantum cryptography steps on the field SemiWiki
PPT Cryptography in a Post Quantum Computing World PowerPoint
Understand How Leading Companies Like Airbus And Aireon Are Securing Their Infrastructure Against Post.
To Propose A Talk, Please Send An Email To Dr.
Learn To Secure Communications, Iot, And Critical Systems Against Quantum Threats.
The Expected Potential Benefits Of Quantum Computing Are Many For Companies In Industries Such As Financial Services And Beyond—But So Are The Potential Complications.
Related Post: